– author: jackp layout: post title: “How to use encryption in Mule” description: “the use of encrypting password with Jasypt in Mule” excerpt_length: 29 tags: [‘jasypt’, ‘mule’, ‘encryption’, ‘decryption’] —
In this example we will use Jasypt in mule to encrypt clear text passwords in property files. But you could use Jasypt to encrypt all sorts of things e.g. encrypt all in a property file and not just the password.
Jasypt is an open source java library which allows the developer to add basic encryption capabilities to their projects with minimum effort, without the need of having deep knowledge on how cryptography works. We use Jasypt to encrypt clear text password in mule property files.
First, you need to download the Jasypt distribution, because we shall use it later to encrypt our password. As of this writing, the latest version is 1.9.2, and you can get it at jasypt.org
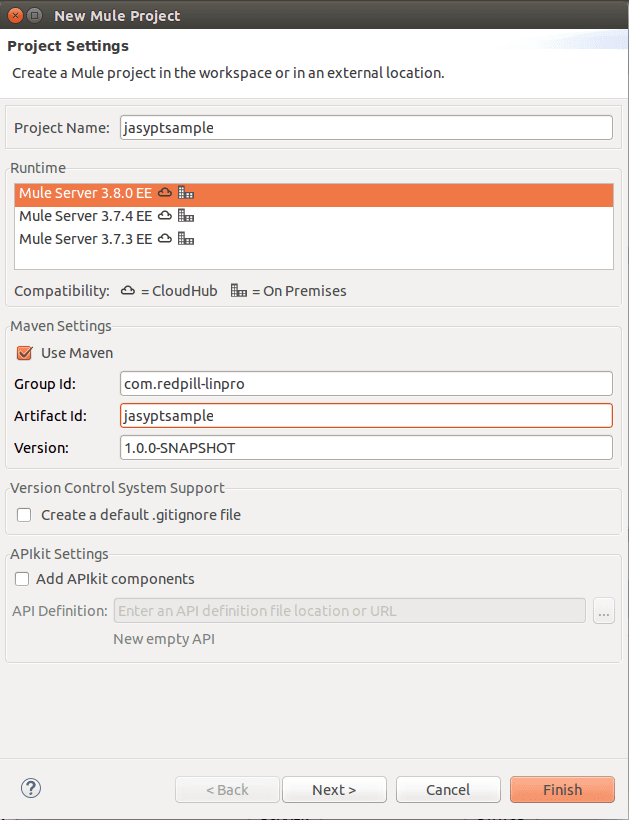
Then start a new mule project with maven support
Open the project pom file and add the following Maven dependencies, this is the dependencies that include the Jasypt libraries.
<dependency>
<groupId>org.jasypt</groupId>
<artifactId>jasypt-spring31</artifactId>
<version>1.9.2</version>
</dependency>
<dependency>
<groupId>org.jasypt</groupId>
<artifactId>jasypt</artifactId>
<version>1.9.2</version>
</dependency>
Next we configure the Jasypt java beans as spring beans in our mule configuration file as the first thing after the namespaces.
<?xml version="1.0" encoding="UTF-8"?>
<mule xmlns:http="http://www.mulesoft.org/schema/mule/http" xmlns:context="http://www.springframework.org/schema/context" xmlns="http://www.mulesoft.org/schema/mule/core" xmlns:doc="http://www.mulesoft.org/schema/mule/documentation"
xmlns:spring="http://www.springframework.org/schema/beans"
xmlns:util="http://www.springframework.org/schema/util"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans-current.xsd
http://www.mulesoft.org/schema/mule/core http://www.mulesoft.org/schema/mule/core/current/mule.xsd
http://www.springframework.org/schema/context http://www.springframework.org/schema/context/spring-context-current.xsd
http://www.mulesoft.org/schema/mule/http http://www.mulesoft.org/schema/mule/http/current/mule-http.xsd">
<spring:beans>
<!-- -->
<!-- Configuration for encryptor, based on environment variables. -->
<!-- -->
<!-- In this example, the encryption password will be read from an -->
<!-- environment variable called "JASYPT_MULE_PASSWORD" which, once -->
<!-- the application has been started, could be safely unset. -->
<!-- -->
<spring:bean id="environmentVariablesConfiguration"
class="org.jasypt.encryption.pbe.config.EnvironmentStringPBEConfig">
<spring:property name="algorithm" value="PBEWithMD5AndDES" />
<spring:property name="passwordEnvName" value="JASYPT_MULE_PASSWORD" />
</spring:bean>
<!-- -->
<!-- This will be the encryptor used for decrypting configuration values. -->
<!-- -->
<spring:bean id="configurationEncryptor"
class="org.jasypt.encryption.pbe.StandardPBEStringEncryptor">
<spring:property name="config" ref="environmentVariablesConfiguration" />
</spring:bean>
<!-- -->
<!-- The EncryptablePropertyPlaceholderConfigurer will read the -->
<!-- .properties files and make their values accessible as ${var}. -->
<!-- -->
<!-- Our "configurationEncryptor" bean (which implements -->
<!-- org.jasypt.encryption.StringEncryptor) is set as a constructor arg. -->
<!-- -->
<!-- The property file should be placed in /src/main/resources -->
<!-- -->
<spring:bean id="propertyConfigurer"
class="org.jasypt.spring31.properties.EncryptablePropertyPlaceholderConfigurer">
<spring:constructor-arg ref="configurationEncryptor" />
<spring:property name="locations">
<spring:list>
<spring:value>jasyptsample.properties</spring:value>
</spring:list>
</spring:property>
</spring:bean>
</spring:beans>
<!-- Here comes your normal flow definition -->
</mule>
Now we encrypt your password, with the Jasypt
distribution you downloaded in the start of this post. [JASYPT_HOME]
is that place where you unpacked the distribution. As an example, my
distribution is located at /home/tools/jasypt/ which then becomes my
[JASYPT_HOME]. Now go to [JASYPT_HOME]/bin and run the following
command:
./encrypt.sh input="thisisjasyptencrypted" password=mymajorsecretpassword algorithm=PBEWithMD5AndDES
Here
input is the password you want to encrypt e.g. the password for your database or similar,password is the super password that Jasypt use to crypt and decrypt your original password andalgorithm is the algorithm of your choice. Jasypt support various algorithm but we stick with PBEWithMD5AndDESThe command should give the following output:
----ENVIRONMENT-----------------
Runtime: Oracle Corporation OpenJDK 64-Bit Server VM 25.91-b14
----ARGUMENTS-------------------
algorithm: PBEWithMD5AndDES
input: thisisjasyptencrypted
password: mymajorsecretpassword
----OUTPUT----------------------
zL37W0sWwPEidfzUfEHCZcHGX9R3u0lh/Tb9jAtmaOc=
If you use this in a Mule Runtime (out of Anypoint Studio), you have to configure an environment variable.
export JASYPT_MULE_PASSWORD=mymajorsecretpassword
or to store the variable permanent write it to /etc/environment file, in a name=value format, e.g. JASYPT_MULE_PASSWORD=mymajorsecretpassword
In the System Properties window, click on the Advanced tab, then click
the Environment Variables button near the bottom of that tab. Then
enter JASYPT_MULE_PASSWORD=mymajorsecretpassword
The JASYPT_MULE_PASSWORD variable can be removed when Mule is started if you feel it will be safer that way.
If you’re uncertain how to create environment variables for your system, then google it or submit a question on stackoverflow.com. Given the many systems and ways to create it, so going through all of them is out of scope for this blog post.
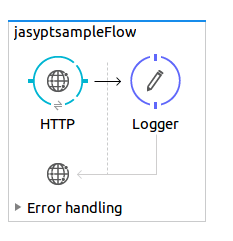
Now we build a test flow so we can test our Jasypt implementation, it is a simple flow with just an HTTP and a logger component. The result should be that the decrypted password is written to the console.
Drag an HTTP component onto the “canvas” and make an HTTP configuration just use the default host 0.0.0.0 and port 8081. In the Logger component just write ${jasypttest} And now you can start the application. Just make sure that this XML code is below the spring bean configuration.
Flow XML:
<http:listener-config name="HTTP_Listener_Configuration" host="0.0.0.0" port="8081" doc:name="HTTP Listener Configuration"/>
<flow name="jasyptsampleFlow">
<http:listener config-ref="HTTP_Listener_Configuration" path="/" doc:name="HTTP"/>
<!-- write the decryptet password to the console -->
<logger message="${jasypttest}" level="INFO" doc:name="Logger"/>
</flow>
The above XML flow should look like this in the visual designer.
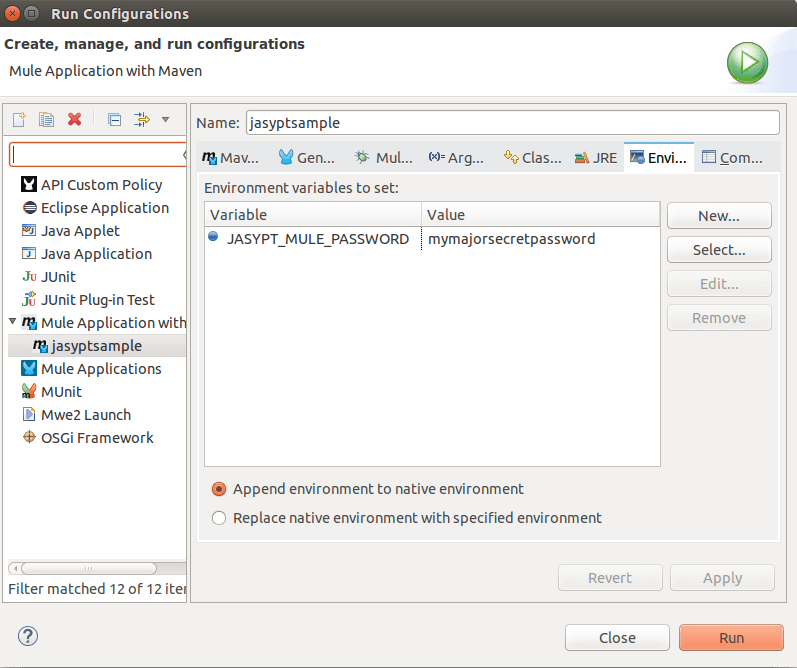
Before starting the flow, you have to set a runtime environment if you are using Anypoint Studio or any other Eclipse-based development IDE. Run -> Run Configurations -> Environment (tab)
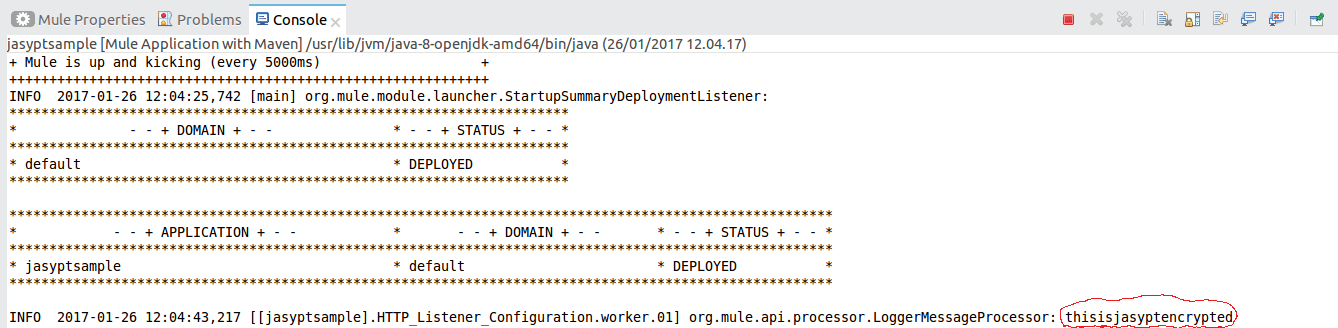
Then you can run the sample application. And go to
http://localhost:8081/ to start the flow we just created. Now
look in the log in Anypoint studio and you can see the decrypted
password (thisisjasyptencrypted).
Be aware of that this solution still has the master password in plain text; the advantage is that you have separated the password to the database, SFTP host or what ever password/property you have encrypted from the development environment. You will have to set the environment variable for every environment you have. Where I came from this was a good solution because the developer does not have access to the servers there were only a few people there has this access and they stood for the password creation and setting up the environment variable and other environment specific properties.
Get the Jasypt Sample project code on GitHub.
Update